In Part 1 of AXEL’s feature on the world’s top hacking groups, we featured some of the leading cultivators of chaos in the world. From state-sponsored groups like Bureau 121 to leaderless hacktivist organizations like Anonymous, no two hacking groups are the same. Each organization has different personnel, goals, and methods of achieving those goals, with some more successful than others. In a way, these criminal syndicates are extremely similar to traditional businesses: If you’re financially successful, your group will flourish. If you struggle to make steady income, you’ll lose employees and, eventually, your entire company.
However, just as it is in the business world, there are some hacking groups that are seemingly too big to fail. Typically, these groups are state-sponsored, and receive oodles of cash for security purposes. While these state-sponsored groups may rarely grab headlines, these are the syndicates that truly hold the most power. After all, an independent hacker group can be taken down with a thorough investigation. A hacker group supported by a powerful nation is extremely unlikely to ever face investigations or oversight from other nations.
These four groups represent some of the most powerful hacking organizations in the world:
Cozy Bear
Cozy Bear is yet another Russian state-sponsored hacking group that focuses on attacking Western governments and media [1]. This group, however, seemingly has an intense focus on the United States. In 2014, the group hacked the State Department and the White House’s email systems, and in 2020, breached the Commerce and Treasury departments [2]. As part of Russia’s foreign intelligence service, Cozy Bear, along with sibling hacking group Fancy Bear, hacked into the Democratic National Committee (DNC) in 2016. Oddly enough, Cozy Bear and Fancy Bear were unaware of each other’s activities, and both independently hacked the political committee [3].
Although Cozy Bear and Fancy Bear both breached the DNC’s servers in 2016, Cozy Bear’s latest actions show that these hacks aren’t done for partisan purposes. In July 2021, the group breached the servers of the Republican National Committee (RNC) [4]. Ultimately this highlights Russia’s main strategy regarding cyberwarfare. The goal isn’t to make sure a certain candidate wins; it’s to undermine faith in the electoral process, thus lowering confidence in the nation itself. While Russia may have a preferred candidate every four years, it’s cybersecurity actions show a clear, nonpartisan strategy to simply embarrass the United States and decrease faith in its political processes. And Cozy Bear is just one of many groups Russia uses to further this goal.
REvil
One of the newest hacking groups in the world is also one of the most notorious. REvil is a private Russian group that makes millions from its ransomware attacks on businesses. The group initially gained attention in May 2020, when it hacked an entertainment-focused law firm and stole a number of files from the firm. REvil threatened then-President Donald Trump to release compromising documents unless the group received a massive USD $42 million ransom [5]. However, cybersecurity researchers quickly believed that this was a bluff, and no compromising documents were ever released by REvil [6].
Unfortunately, REvil’s initial failure did not deter the group. In 2021, the group was responsible for two massive cyberattacks. First, in May 2021, REvil breached JBS Foods, the world’s largest beef producer. This attack forced the company to shut down some of its food processing plants, threatening a potential beef shortage. However, just one day after the initial attack, JBS paid a USD $11 million ransom to REvil to decrypt its servers [7]. While the quick payment ensured there would be no major shortages, it showed how desperate businesses can be if hit with a devastating ransomware attack. Just a month later, REvil attacked Kaseya, a networks, systems, and IT software company. This attack shut down Kaseya’s main software, ultimately affecting up to 1,500 businesses worldwide. The impacts of this attack were felt worldwide, with a Swedish grocery store chain closed because of inoperable cash registers, and New Zealand schools being taken offline [8].
Thankfully, in October 2021, REvil itself was forced offline by a multi-country operation led by the United States [9]. While this doesn’t mean REvil will never pop up again, the crackdown on ransomware shows that even the most notorious private hacking groups can be stopped.
Chinese Cyber Operations
While not much is known about China’s cyber operations, we do know that their attacks have been effective. In 2010, China was the culprit behind Operation Aurora, an advanced, highly-sophisticated attack on dozens of American companies, including Google and Adobe [10]. In the attack, China stole intellectual property, along with access to the Gmail accounts of two high-profile human rights activists.
Following this complex cyberattack, China was accused of executing one of the worst cyberattacks of all time: The Equifax data breach. In February 2020, the United States charged four members of China’s People’s Liberation Army with the 2017 hack that leaked personal information of over 150 million Americans [11]. While the United States has no way of extraditing the four soldiers for trial, this claim highlighted the sheer power of state cyber operations groups. The Equifax hack had a profound effect on everyday Americans, and caused concern that extremely effective and damaging cyberattacks could become commonplace in the future.
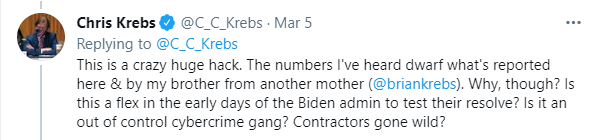
In the present, China’s cyber operations have expanded. This escalation is fueled by the desire for more intelligence, particularly from the United States amid rising tensions between the two global superpowers [12]. In fact, Western governments have accused China of hacking into Microsoft’s Exchange company server. This hack affected about 250,000 organizations worldwide, allowing Chinese hackers to pilfer through company emails for intelligence. While this hack was not nearly as impactful as the Equifax breach, it highlights China’s renewed focus on gathering massive amounts of intelligence on the United States and other Western nations.
NSA Tailored Access Operations
While many of the world’s top hacking groups operate far from North America, the world’s most powerful group is undoubtedly within American borders. The National Security Administration’s (NSA) Tailored Access Operations group gathers intelligence from foreign targets by hacking into devices, stealing data, and monitoring communications. Additionally, the group develops software that can destroy a foreign target’s computer and networks [13]. The group is responsible for developing malware that targeted Iran’s nuclear program, along with regularly breaching Chinese computer networks for gathering intelligence.
The United States’ targeted surveillance capabilities should come as no surprise. After all, the NSA is well-known for its mass surveillance techniques. Tailored Access Operations is relatively similar to other state cyber operations groups: It uses targeted surveillance to gather intelligence, and uses sophisticated malware to attack its targets. Of course, because it’s the NSA, there is the possibility that the group has even more publicly unknown high-tech resources for cyberattacks. While Tailored Access Operations works in the shadows, the strength of the NSA, and the United States in general, make this group the most powerful hackers in the world.
About AXEL
Some of these powerful hacking groups will, unfortunately, continue to wreak havoc in 2022. That’s why data security and user privacy remain as important as ever. At AXEL we believe that privacy is a human right, and that your information deserves the best protection. That’s why we created AXEL Go. AXEL Go uses 256-bit encryption, blockchain technology and decentralized servers to ensure it’s the best file transfer software on the market. Whether you need cloud video storage or cloud file management, AXEL Go is the secure file hosting solution. If you’re ready to try the best file sharing app for PC and mobile devices, try two free weeks of AXEL Go here.
[1] Meyer, Josh. “Cozy Bear Explained: What You Need to Know about the Russian Hacks.” NBCNews.com. NBCUniversal News Group, September 15, 2016. https://www.nbcnews.com/storyline/hacking-in-america/cozy-bear-explained-what-you-need-know-about-russian-hacks-n648541
[2] Nakashima, Ellen, and Craig Timberg. “Russian Government Hackers Are behind a Broad Espionage Campaign That Has Compromised U.S. Agencies, Including Treasury and Commerce.” The Washington Post. WP Company, December 14, 2020. https://www.washingtonpost.com/national-security/russian-government-spies-are-behind-a-broad-hacking-campaign-that-has-breached-us-agencies-and-a-top-cyber-firm/2020/12/13/d5a53b88-3d7d-11eb-9453-fc36ba051781_story.html
[3] “Bear on Bear.” The Economist. The Economist Newspaper, September 22, 2016. https://www.economist.com/united-states/2016/09/22/bear-on-bear
[4] Turton, William, and Jennifer Jacobs. “Russia ‘Cozy Bear’ Breached GOP as Ransomware Attack Hit.” Bloomberg.com. Bloomberg, July 6, 2021. https://www.bloomberg.com/news/articles/2021-07-06/russian-state-hackers-breached-republican-national-committee
[5] Collier, Kevin, and Diana Dasrath. “Criminal Group That Hacked Law Firm Threatens to Release Trump Documents.” NBCNews.com. NBCUniversal News Group, May 16, 2020. https://www.nbcnews.com/tech/security/criminal-group-hacked-law-firm-threatens-release-trump-documents-n1208366
[6] Vanian, Jonathan. “Everything to Know about Revil, the Group behind Several Devastating Ransomware Attacks.” Fortune. Fortune, July 8, 2021. https://fortune.com/2021/07/07/what-is-revil-ransomware-attack-kaseya/
[7] Abrams, Lawrence. “JBS Paid $11 Million to REvil Ransomware, $22.5m First Demanded.” BleepingComputer. BleepingComputer, June 10, 2021. https://www.bleepingcomputer.com/news/security/jbs-paid-11-million-to-revil-ransomware-225m-first-demanded/
[8] Satter, Raphael. “Up to 1,500 Businesses Affected by Ransomware Attack, U.S. Firm’s CEO Says.” Reuters. Thomson Reuters, July 6, 2021. https://www.reuters.com/technology/hackers-demand-70-million-liberate-data-held-by-companies-hit-mass-cyberattack-2021-07-05/
[9] Bing, Christopher, and Joseph Menn. “Exclusive Governments Turn Tables on Ransomware Gang Revil by Pushing It Offline.” Reuters. Thomson Reuters, October 21, 2021. https://www.reuters.com/technology/exclusive-governments-turn-tables-ransomware-gang-revil-by-pushing-it-offline-2021-10-21/
[10] Zetter, Kim. “Google Hack Attack Was Ultra Sophisticated, New Details Show.” Wired. Conde Nast, January 15, 2010. https://www.wired.com/2010/01/operation-aurora/
[11] Perez, Evan, and Zachary Cohen. “US Charges 4 Members of Chinese Military with Equifax Hack.” CNN. Cable News Network, February 11, 2020. https://www.cnn.com/2020/02/10/politics/equifax-chinese-military-justice-department/index.html
[12] Sabbagh, Dan. “Experts Say China’s Low-Level Cyberwar Is Becoming Severe Threat.” The Guardian. Guardian News and Media, September 23, 2021. https://www.theguardian.com/world/2021/sep/23/experts-china-low-level-cyber-war-severe-threat
[13] Peterson, Andrea. “The NSA Has Its Own Team of Elite Hackers.” The Washington Post. WP Company, August 29, 2013. https://www.washingtonpost.com/news/the-switch/wp/2013/08/29/the-nsa-has-its-own-team-of-elite-hackers/