Since March of last year, Russia has been deploying troops close to the Russia-Ukraine border [1]. While troop movement within a nation is typically normal, Russia’s relationship with Ukraine is anything but. Since 2014, Russia has aggressively shown its desire to annex Ukrainian territory, starting with its occupation of Crimea, a territory that was formerly part of Ukraine, but mostly comprised of people of Russian ethnicity. However, it soon became clear that Crimea was just the beginning for Moscow’s leaders. Following Russia’s occupation of Crimea in 2014, the country began to use unique, digital strategies to destabilize Ukraine.
Beginning in 2015, Russia has engaged in flagrant cyberwarfare with Ukraine. And these attacks weren’t just data breaches and ransomware attacks; they’ve affected nearly every resident of Ukraine. Ultimately, the Russia-Ukraine conflict could be a sneak peek of how war is waged in the future.
Hackers Target Ukraine
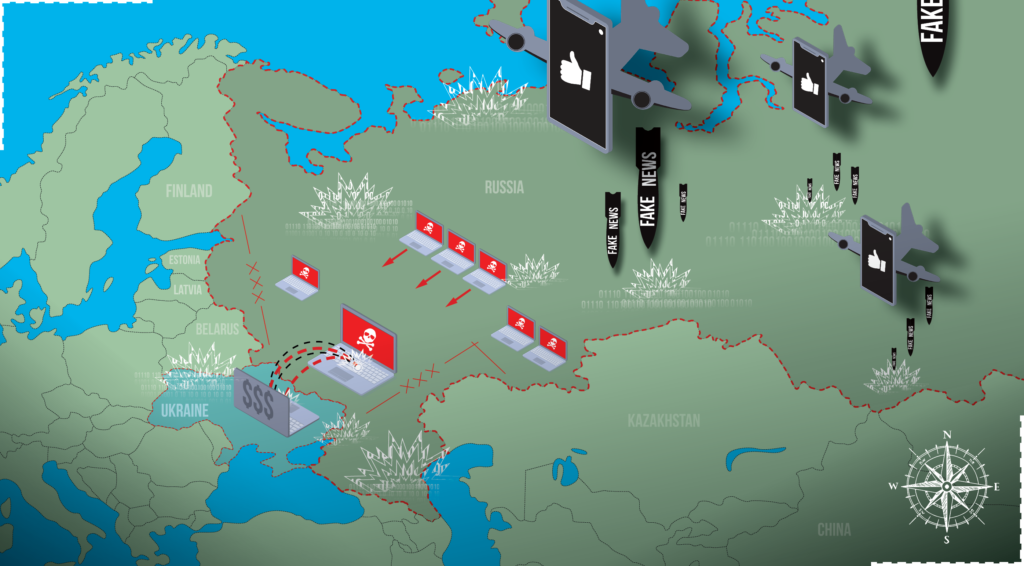
Following Russia’s annexation of Crimea, Ukraine saw relative calm for almost two years. However, in December 2015, Russia launched an effective, atypical attack. On December 23, a Russian cyber-military unit, “Sandworm,” attacked Ukraine’s power grid, and knocked out electricity to over 200,000 Ukrainians.[2] Thankfully, power was restored to most places within six hours. Although a few hours without electricity isn’t exactly a devastating attack, it was undoubtedly worrying. After all, this was the first-ever confirmed hack that took down a power grid.[2] Additionally, power grid control centers were still not fully operational over two months after the attack, highlighting the sheer strength and organization of the attack.
Unfortunately, this was not the only cyberattack that Russia has executed on Ukrainians. One year later, in December 2016, Russia again attacked Ukraine’s power grid.[3] They quickly followed up by targeting Ukrainian banks and state-owned industries in June 2017.[4] Following this major attack, Russia seemed to calm down, and tensions actually diffused for a few years. However, this changed in early 2022. As Russia began to mobilize its troops toward the Ukraine border, Moscow launched another cyberattack. This time, Russians were able to take down over 70 Ukrainian government websites, along with a message that warned Ukrainians to “Prepare for the worst.”[5]
Although Russia launched multiple effective cyberattacks, many cybersecurity experts believe Russian President Vladimir Putin could have ordered the attacks to be so much worse. After all, Ukraine’s 2016 power grid outage only lasted for about an hour. This made some believe that Russia was using Ukraine as a “testbed” for refining cyberattacks that could be used globally[3]. No matter Russia’s ultimate purpose, these cyberattacks show a glimpse of Russia’s unique military strategy.
Disinformation Campaigns
In addition to cyberattacks, Russia has also used the Internet to sew instability within Ukraine as well. When Russia invaded Crimea in 2014, the country used state media and social media to sway ethnic Russians in Ukraine to support the annexation.[6] These accounts falsely alleged that Western forces manipulated Ukrainian protests, and also fabricated stories of Ukrainian soldier misconduct. Using this disinformation, Russia was able to gain enough support to annex Crimea with (relatively) little pushback.
If these disinformation efforts sound familiar, well, they are. Russia used similar techniques to meddle in the United States’ 2016 presidential election.[6] It’s a sinister, yet successful strategy for promoting Russian interests. With the emergence of the Internet and the popularity of social media, information warfare is relatively simple. Being able to kindle instability from thousands of miles away is a new, anxiety-inducing strategy that is being utilized in Ukraine, the United States, and other nations. Although it may not lead to traditional warfare casualties, Russia’s cyberwarfare actions have been extremely successful in promoting Putin’s interests.
What Would a Cyberwar Look Like?
When people think of cyberattacks, most think of data breaches and ransomware attacks. Damaging, yes, but they typically don’t harm anyone outside of the affected business and its customers. Cyberwarfare is very different. While Russia’s power grid attacks on Ukraine were effective, they were not nearly as devastating as they could have been. If Russia chooses to execute full-strength cyberattacks, the consequences could be deadly. In this scenario, Russia could shut off most of the country’s electricity, disable heat in the middle of winter, and shut down Ukraine’s military communications.[7] A cyberattack like this could make it astonishingly easy for Russia to successfully invade Ukraine. While an attack of this magnitude has not been undertaken by Russia or any other nation, the possibility of one is undoubtedly concerning. Full-fledged cyberwarfare is something the world has never seen, but the possibility of it increases every day.
Of course, it’s naive to assume that Russia is the only country preparing for cyberwarfare. The United States certainly has the capability to defend itself against cyberwarfare, and the ability to execute offensive cyberattacks. In fact, the United States was one of the first nations to engage in an act of cyberwarfare. In 2010, the U.S. and Israel jointly infected Iran’s nuclear infrastructure with the Stuxnet computer worm.[8] This attack crippled Iran’s nuclear program, highlighting just how successful cyberattacks can be.
When it comes to cyberwarfare, we really don’t know what the rules are yet. If Russia attacks another nation’s electricity or heat, indirectly leading to civilian deaths, is that a war crime? Or is remotely targeting infrastructure fair game? There are dozens of questions that haven’t been answered. Unfortunately, we may learn these answers during a future cyberwar. Whether this new kind of war is waged between Russia and Ukraine, the U.S. and China, or some other combination of unfriendly nations, we know the consequences of cyberwarfare will be severe.
About AXEL
Cybercrime is an ever-present threat. Thankfully, AXEL makes it easy to protect yourself from ransomware and data breaches. At AXEL, we believe that privacy is a human right, and that your information deserves the best protection. That’s why we created AXEL Go. AXEL Go uses 256-bit encryption, blockchain technology and decentralized servers to ensure it’s the most secure file transfer software on the market. Whether you need to transfer large files or send files online, AXEL Go is the best cloud storage solution. If you’re ready to try the most secure file-sharing app for PC and mobile devices, get two free weeks of AXEL Go here.
[1] Roth, Andrew. “EU and UK Pledge Backing to Ukraine after Russian Military Buildup.” The Guardian. Guardian News and Media, April 6, 2021. https://www.theguardian.com/world/2021/apr/05/eu-sounds-alarm-at-russian-troops-ukraine-border-moves
[2] Zetter, Kim. “Inside the Cunning, Unprecedented Hack of Ukraine’s Power Grid.” Wired. Conde Nast, March 3, 2016. https://www.wired.com/2016/03/inside-cunning-unprecedented-hack-ukraines-power-grid/
[3] Zetter, Kim. “The Ukrainian Power Grid Was Hacked Again.” VICE, January 10, 2017. https://www.vice.com/en/article/bmvkn4/ukrainian-power-station-hacking-december-2016-report
[4] Polityuk, Pavel, and Alessandra Prentice. “Ukrainian Banks, Electricity Firm Hit by Fresh Cyber Attack.” Reuters. Thomson Reuters, June 27, 2017. https://www.reuters.com/article/us-ukraine-cyber-attacks-idUSKBN19I1IJ
[5] “Ukraine Cyber-Attack: Russia to Blame for Hack, Says Kyiv.” BBC News. BBC, January 14, 2022. https://www.bbc.com/news/world-europe-59992531
[6] Merchant, Nomaan. “US Tries to Name and Shame Russian Disinformation on Ukraine.” ABC News. ABC News Network, January 28, 2022. https://abcnews.go.com/Politics/wireStory/us-shame-russian-disinformation-ukraine-82526617
[7] Miller, Maggie. “Russian Invasion of Ukraine Could Redefine Cyber Warfare.” POLITICO, January 28, 2022. https://www.politico.com/news/2022/01/28/russia-cyber-army-ukraine-00003051
[8] Melman, Yossi. “’Computer Virus in Iran Actually Targeted Larger Nuclear Facility’.” Haaretz.com. Haaretz, September 28, 2010. https://www.haaretz.com/1.5118389.